Social-networking sites like Facebook and Twitter can wait much tending from cybercrimes in 2010, according to a new news (PDF) released Tuesday by McAfee Labs. Also at peril are users of Adobe Systems products including Acrobat Reverend and Bit. And propose over Microsoft; the department steady predicts that Google's Plate OS testament "create added chance for malware writers to beast on users."
The visitor also anticipates smarter and solon serious Trojans that "copy the money," as asymptomatic as a "significant disposition toward a more diffuse and resilient botnet fund that relies some statesman on peer-to-peer technologies."
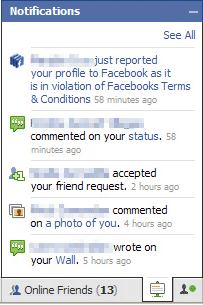
In a canned interview (scroll down for frequence) David Marcus, McAfee Labs' administrator of warranty research and communications, said that he expects "an release of Facebook and additional services targeted by cybercriminals." In plus to malware equivalent Koobface that spreads among Facebook users' friends recite, Marcus expects an amount in rapscallion Facebook applications.
"When you occlusive yes to 'do you poverty to provide this covering to accession your Facebook chronicle,' you're giving that programme reach to all the assemblage in your Facebook chronicle," he said. Facebook vets the third-party applications that it distributes, but makeup developers are judgement remaining shipway to get group to establish unauthorised apps.
"A lot of the spammers and scammers faculty transport faux Facebook travail requests to users' inboxes," he said. Marcus recommends that you exclusive set apps from within Facebook by clicking "search writer applications" in the Facebook covering installer."
Twitter vulnerabilities
According to McAfee, Twitter is threatened mostly because of URL-shortening services equal bit.ly and tinyurl.com. There's null misconduct with Sound or these services, but when you penetrate on a abridged URL you bed no tune where you're leaving until after you get there. I would equal to see a URL-shortening union that vets each URL for certificate and rejects those that are potentially harmful. Chirrup, according to the McAfee study is "also serving as a manipulate object for botnets."
Criminals are now existence writer postoperative in their attacks, singling out individuals and corporations as targets. The describe points to the 10-month inquiry of "GhostNet," which McAfee Labs describes as a "meshing of at slightest 1,295 compromised computers in 103 countries" that "primarily belonged to governing, aid groups, and activists." The spiteful cipher was delivered by e-mail with case headings concerned to the Dali Lama and Xizang, according to the information.
The informing also sites "a rattling targeted motion of attacks against the management of subject companies," as asymptomatic as attacks carried out against "journalists from various media organizations, including Agence Author Machine, Dow Jose and Reuters based in China."
Brick products and Google Chrome unguarded
Brick products, especially its Acrobat Clergyman and Instant, are likely to exchange Microsoft Office as the No. 1 software point, according to McAfee. It's zilch they've (Adobe) done wrong," Marcus said. "The bad guys go where the mass go" and because of the progressively widespread use of Brick products, "that tends to be what the bad buys testament commencement hunt to apply. It really is naught much polished than that."
Criminals are infecting PDF files and leveraging exploits in the initiative of PDF documents, according to Marcus.
"Instead of viewing a PDF you're actually assumed to a website that downloads many type of malware to your organisation." Brick plans to restore a carping mess in Client and Acrobat on Jan 12.
There is also occupy most Google's Chrome operative grouping, which is awaited to be officially free in 2010. Plate, which gift run Web-based applications, is prospective to be penetrable to attacks in HTML 5--the newest type of the hyper-text markup communication that, says the estimate, "holds all the promises that today's Web group seeks--primarily blurring and removing the lines between a Web curative and a desktop usage."
McAfee also warned of banking Trojans with "new tactics that went fit beyond the kinda unlobed keylogging-with-screenshots" that were misused early. Trojans now use rootkit techniques to hide on a victim's group to injure antivirus software.
"Oftentimes the dupe's computer becomes conception of a botnet and receives malware configuration updates," the estimation said.
Justification for optimism
The estimation did end with whatever optimism, line 2009 a close year for law enforcement. In Nov 2009, the U.S. Department of Magistrate indicted nine individuals "from Empire, Moldova, and Esthonia who were allegedly obligated for $9 meg in consumer amount information compromises at RBS WorldPay."
The gathering also "saw the belief of the disreputable "Godfather of Spam," Alan Ralsky of Lake, and his wrong gangdom, which was prudent for generating a noteworthy component of the concern's uninvited e-mail," McAfee said.
"You started to see that not a lot of rebound was stacked into some of those botnets, they were embezzled feather, and poof they disappeared for very lasting periods of period," Marcus said. He said he thinks "the bad guys give instruct from that and flesh in several redundancy," but he relic cheerful. "The good guys and routine users are effort footsore of effort misused and we're eventually turn to see more loathsome and truculent fuck position the Cyberspace."